One of the most amazing security encounter i faced in my throughout career was of the Hall of Fame by Get Pocket. A quite unexpected Hall Of Fame. I usually wrote less about bug story and more about vulnerabilities in my previous posts. But today, i am going to explain a case about how i got Get Pocket Hall Of Fame Q2- 2015 .
“Pocket, previously known as Read It Later, is an application and service for managing a reading list of articles from the Internet.”
So i was trying to find out vulnerability on Pocket’s official site before 2 months, and i went through the login page and found a weak token for form_check which wasn’t effective as i thought. I tried to bypass and Brute it down using a bypass redirection logic. So initially, i wrote a simple Bruter script and tried to load my wordlist and got prepared for directory attack on the login.
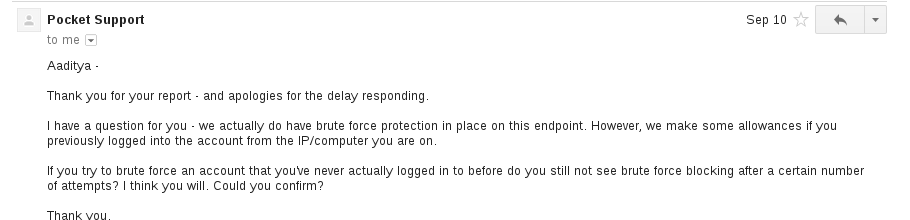
And i performed rate limiting tests by using my various methods on my ID, and fortunately it didn’t locked me out at all. So instantly i reported to the Pocket’s security team before 2 months. And after 4 days i got a response
Okay . 😦 So, it’s triaged actually. The Security Engineer told me that that have Brute force protection on that EndPoint using a flag form_check, and they told me that if i would brute on an another account which hasn’t been logged in ever from my IP , i’ll need to Bypass it. I used some Logics yet and same mentioned stuff and this time i had anonymous@gmail.com ID as a target .
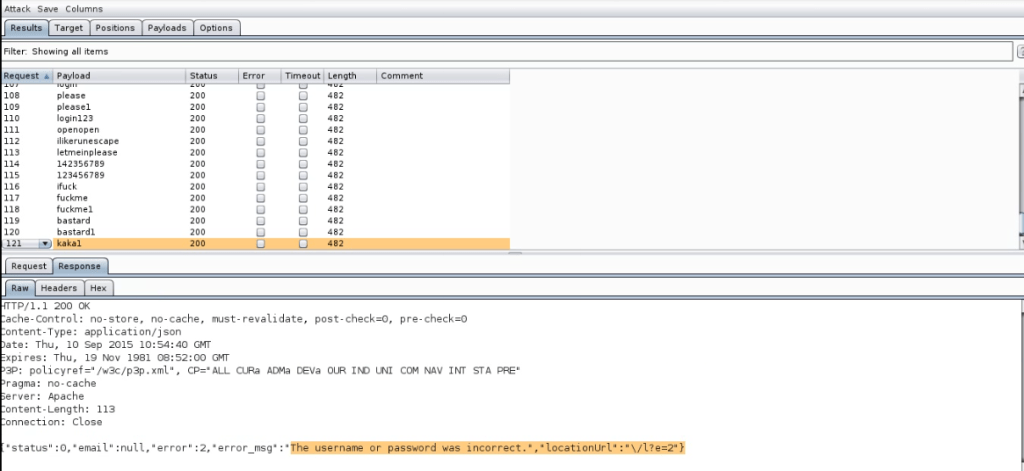
Okay, having some good points, i worked again on it and carried out a few tests.
BAAAM. Again Worked. I cracked the password at 867th trial (Cant disclose due to security purpose). The above pic is screenshot i took from POC live video which i sent to team and hoped for the best.
After 15 days, i got reply by their team that, It’s good that you bypassed a user id, but can you bypass our special id bruteforce1@getpocket.com. We are sure, it will be protected.
Immediately i tried my test again on my Scripts and Live Proxies by using the same Request Link Bypass method, and was amazed to see the flag form was improved 😮 . Still, i ran my tests and efforts on it. But what i got was a block after 3 request.
Response : error_msg = “You are trying too often. Your IP Has been blocked”
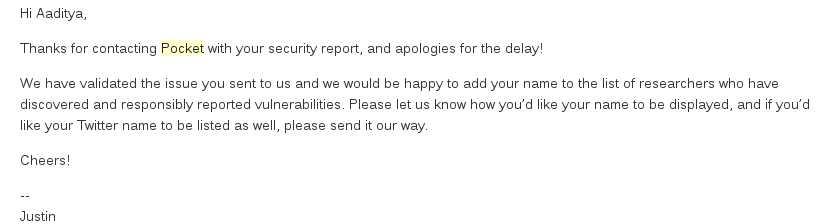
My all previous test were done when i bypassed the check flag, but this was something different. I tried to research and break the cookie to rule em over. Mission STARTED. I tried testing on three different id : User already logged in with the IP Before, User who hasn’t logged in from that before and Team’s Email Address. Surprised to find out, all used check_form there. Then i thought if i could play or brute the encryption algorithm even 😛 The most evil idea was obviously needed at that time. Made a mapping and found a form check bypass method . So i made two directory and tried to test fingers crossed, and as old man says “Hardwork pays off sooner or later”. BAAM it worked. I ran test till a longer period of time and quickly sent them password. (Hint: I used rockyou.txt) . Then i waited for reply and before 2 days i got this
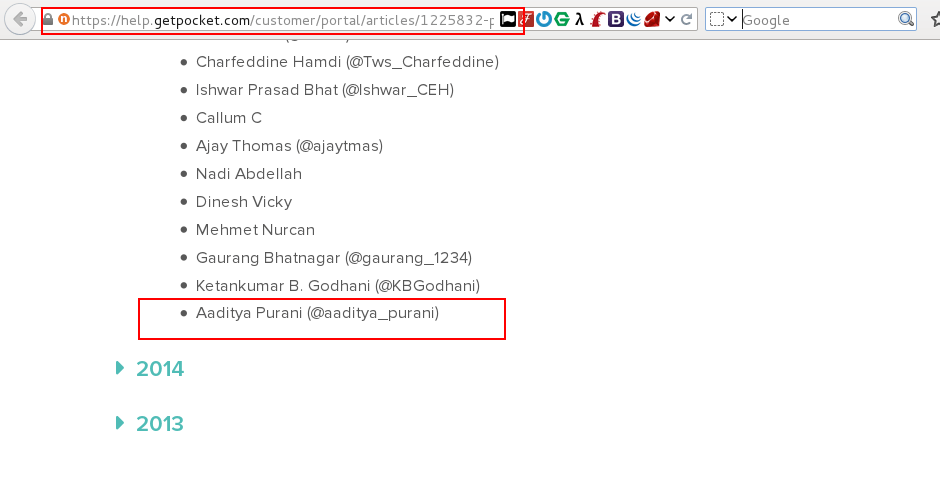
BAAAAAAMMM.. I am In. How i felt after they added my name in their Hall of fame
Hall of fame link : https://help.getpocket.com/customer/portal/articles/1225832-pocket-security-overview
20th Acknowledgment it was. I don’t write much about my Bug Reports, but as this was a game of puzzle, I thought to make it online.
Do Bookmark the website, and follow me on https://twitter.com/aaditya_purani for more.
Thanks.









Leave a comment