CTF’s:
CTF are known as Capture The Flag competition. CTF’s are game designed for students, and professionals which teaches Information Security by asking them to solve challenges which are created in a safe and enclosed environment. In a regular jeopardy style CTF competition, there are various categories – such as – Web, Mobile, Cryptography, Forensics, Binary (some organizers call it as pwn), Reverse Engineering, Misc. There are usually challenges which vary from different points within such categories. Once, a team or individual solves them, they validate a flag which proves they indeed solved it and receive points. The team with highest points under defined amount of time is declared winner. It is a very fun way to learn cybersecurity within enclosed environment. CTF’s for an Information Security Enthusiast is an equivalent of competitive programming (ACM) for a developer. 🙂
I play CTFs from team Perfect Blue , here is our CTFTime Profile. perfect blue finished worldwide top-1 in rankings for the CTF teams in the year 2020 and 2021.
Top Results:
Google CTF 2021 – 1st Rank – Perfect Blue
HITCON CTF 2020 – 1st Rank – Perfect ⚔️ Guesser
HackLu CTF 2020 – 1st Rank – Perfect Blue
Dragon CTF 2020 – 1st Rank – Perfect ⚔️ Guesser
BSides SF 2017, 2018, 2019, 2020 – 1st Rank
GCCS Finals 2017 – 1st Rank
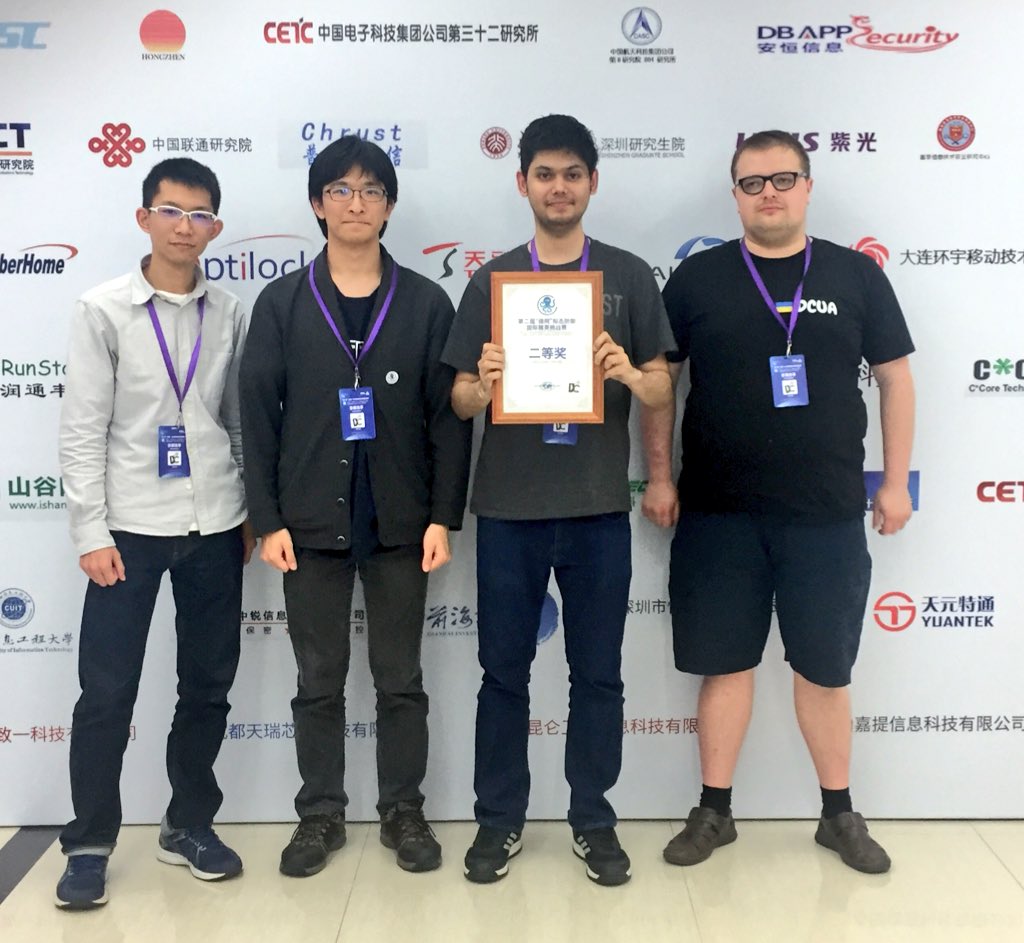
Cyber Mimic Defense China 2019 – 2nd Rank
Some of my on-site Highlights:
Winner of BSides San Francisco CTF 2019 sponsored by Facebook and Google.
Winner of BSides DFW 2018 CTF sponsored by PrevadeLLC. Scored 1000 points, highest ever on that platform
Winner of GCCS – New Delhi, India. (along with romanking98) Award from Indian Prime Minister (Global Conference on Cyber Space) – IT CTF (2017)
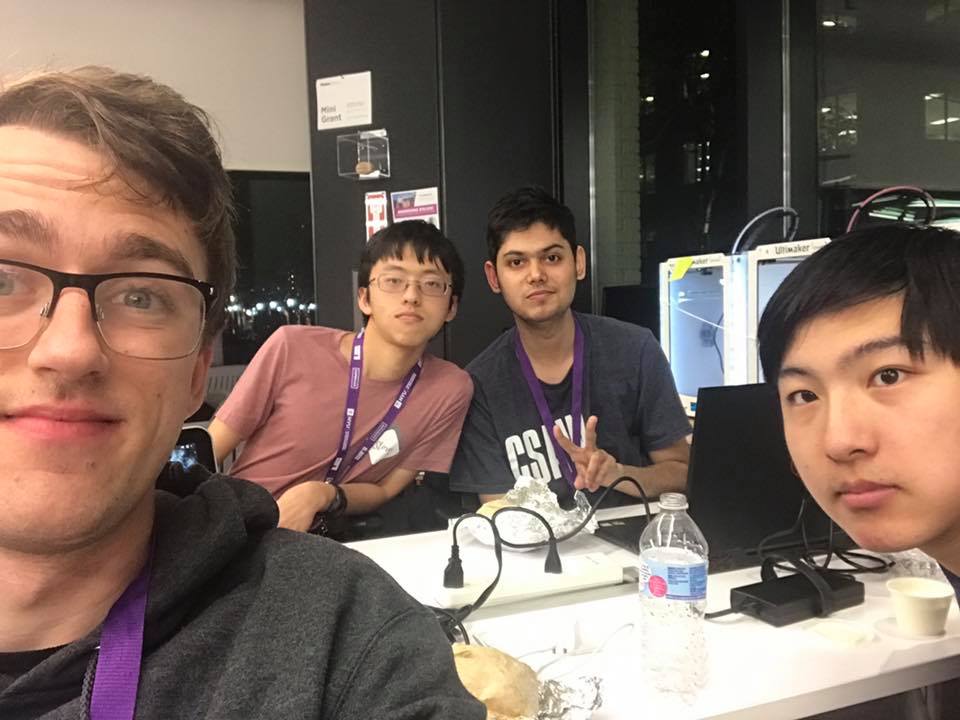
Finalist in CSAW CTF 2018 – NYU, Brooklyn (Finished 6th World-wide in Finals, US Rank 3rd in Qualifiers) along with theKidOfArcrania, DarkZephyrus and c4pkirk
Finalist in CSAW CTF 2017 – NYU (Finished 4th in Quals US-wide)
MIT-CTF 2017 (Cambridge, MA)
Bug Hunting:
It’s great to Help Companies and helping world making a safer place. As an ethical security researcher, it is my duty to help companies and firms protect their asset. (Not routinely updated)
https://www.google.com/about/appsecurity/hall-of-fame/distinction/ (Page 22)
https://www.atlassian.com/security/hall-of-fame
https://secure.sony.net/hallofthanks
https://support.apple.com/en-us/HT201536
http://ca.blackberry.com/enterprise/products/incident-response-team.html#security-updates
https://transloadit.com/security/
https://support.bitcasa.com/hc/en-us/articles/202210658-How-To-Responsibly-Report-Security-Concerns
http://www.owaspacademy.com/security ( 2 Times)
https://hackerone.com/ruxit/thanks
https://hackerone.com/ubnt/thanks
https://hackerone.com/zomato/thanks
https://hackerone.com/localtapiola/thanks
https://hackerone.com/xero/thanks
https://hackerone.com/badoo/thanks
https://www.avast.com/bug-bounty
https://skytv.custhelp.com/app/answers/detail/a_id/1797/~/responsible-disclosure-guidelines
http://blog.teamtailor.com/vulnerability-and-security-reporting/
https://www.onelogin.com/whitehat
https://www.fluxiom.com/security
http://help.getpocket.com/customer/portal/articles/1225832-pocket-security-overview